Information Security
Setting up data and network security
INFORMATION SECURITY
Audit, development, and implementation of turnkey security projects based on the ISO 27001 protocol.
PERIMETER PROTECTION
Perimeter protection and DMZ building from Fortinet, Cisco, Checkpoint.
BACKUP
Setting up backup and restore policy.
NETWORK SECURITY
Network security setting up with dynamic segmentation technology from ArubaOS and providing controlled connectivity with Aruba ClearPass.
CONSULTING SERVICES
Assistance in the implementation of information security processes.
AUTOMATED SECURITY MONITORING
Monitoring of the state of information security objects and building SOC. Control over end devices using End-Point solutions.
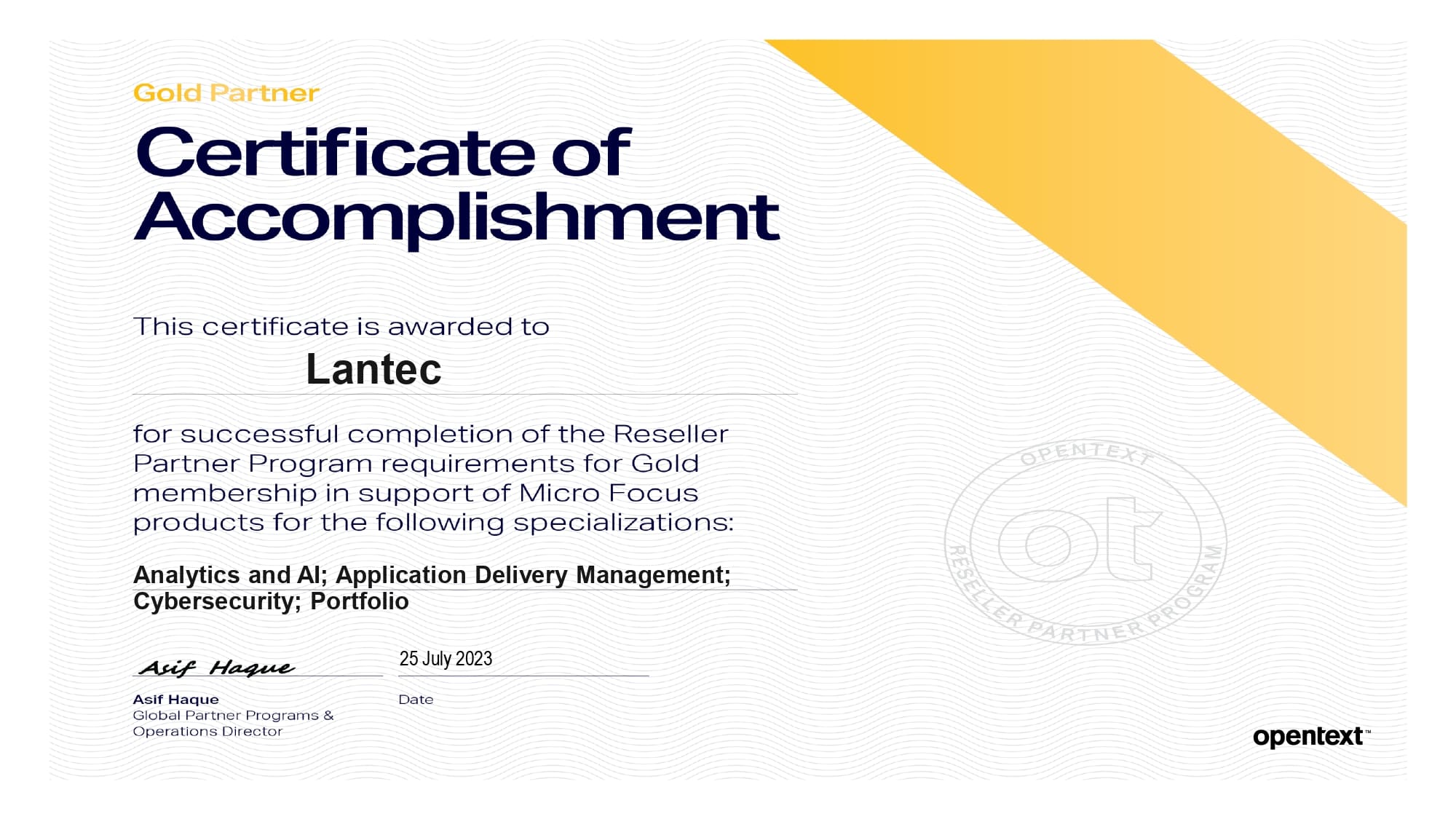
Partner statuses
The company's experience in this area
is confirmed by the following statuses:
Maturity Levels of Enterprise Information Security
First level
Processes are implemented ad hoc and without any methodology
Control level
There are a certain number of non-standardized processes
Identified level
Processes are documented and communicated to stakeholders
Quantitatively managed level
Processes are objects of monitoring and measurement
Optimization level









.png)